A recent analysis has revealed that North Korean hackers have overall stolen $3 billion in crypto heists. Half of these funds have reportedly been used to fund North Korea’s “ballistic missile program,” which was developed in tandem with its nuclear weapons.
Also Read: North Korea Takes Top Spot for 2022 Crypto Thefts
It is a known fact that North Korea has been at the center of orchestrating financial hacks. Several high-profile heists have been linked to the country. In fact, as reported recently, North Korean hackers stole the most digital assets in 2022 when compared to other countries.
South Korean hackers were “really early” into crypto
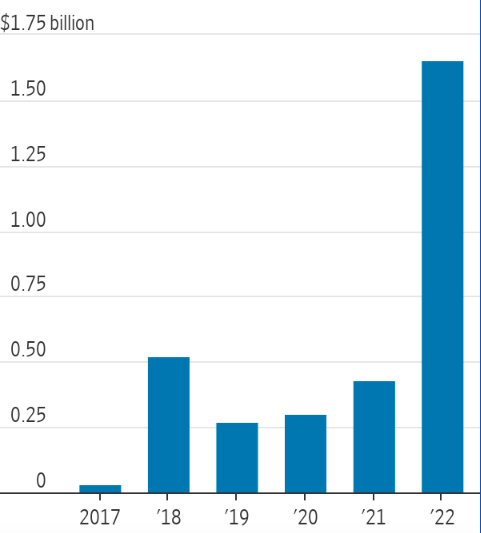
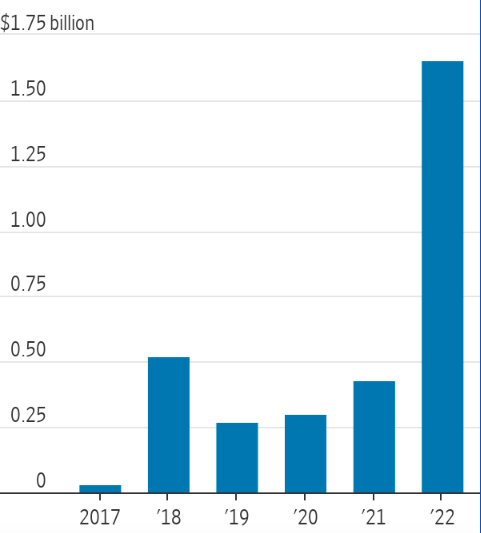
The WSJ report highlighted that North Korea’s hackers started rolling crypto attacks around 2018. Since then, North Korea’s missile launch attempts and successes have only increased. More than 40 incidents were registered in 2022. According to Erin Plante, the Vice President of Investigations with Chainalysis,
“They were really early into crypto, and they were some of the most advanced users of crypto early on.”
Also Read: Crypto: Google is Offering $1 Million for Mining Attack Protection
Nevertheless, U.S. officials have warned that “so much is unknown” about North Korea’s sources of funds amid Western sanctions. Thus, it is almost impractical to arrive at a conclusion, about the role crypto heists play in the increased rate of missile tests. However, the WSJ report underlined that the “test buildup by Kim Jong Un’s reclusive regime has occurred at the same time as a concerning upswing in crypto heists.”
Incidents like the $600 million Sky Mavis episode managed to garner the attention of regulators. According to Anne Neuberger, President Biden’s Deputy National Security Adviser for Cyber and Emerging Technology,
“The real surge in the last year has been against central crypto infrastructure around the world that hold large sums, like Sky Mavis, leading to more large-scale heists. That has driven us to intensely focus on countering this activity.”
Furthermore, Neuberger said that roughly 50% of North Korea’s foreign currency funding for purchasing foreign components for its missile program is now supplied by the regime’s cyber operations. That reportedly marked a sharp rise from earlier estimates, where the figure stood at around 33% of overall funding for the programs.
South Koreans pretend to be Canadian IT workers, Japanese blockchain devs, govt. officials
According to U.S. officials, North Korea has built a “shadow workforce” of thousands of IT workers. They operate in countries like Russia and China. They make money, at times more than $300,000 a year, by doing “mundane technology work.” However, according to investigators, this workforce is often associated with the regime’s cybercrime operations.
In fact, they’ve gone to the extent of pretending to be Canadian IT workers and freelance Japanese blockchain developers. Parallelly, North Koreans have also acted to be government officials. Furthermore, they’ve conducted video interviews to get a job. The report highlighted,
“To get hired by crypto companies, they will hire Western “front people”—essentially actors who sit through job interviews to obscure the fact that North Koreans are the ones actually being hired. Once hired, they will sometimes make small changes to products that allow them to be hacked, former victims and investigators say.“
Also Read: Crypto: Instagram, Twitter, TikTok, YouTube Attacked in EU Advertising Complaint